Cloud Foundry How Tos - Decrypt Backing Service Backup¶
This page describes how to decrypt a Backing Service backup file in case a local copy is needed.
Create and Download Backup File¶
By default, backup files are encrypted with a secret key generated by the Backup Manager.
To be able to download a performed backup, you first have to set a personal encryption key. Otherwise, a performed backup is not downloadable.
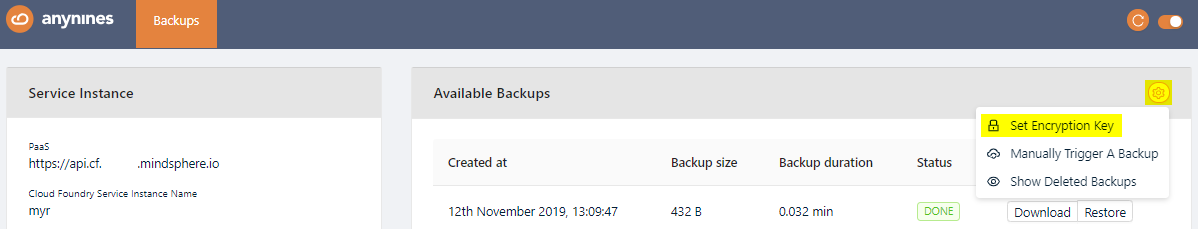
To set a personal encryption key, open the Service Dashboard for the appropriate Service Instance. Click the Setting icon and Set Encryption Key button.
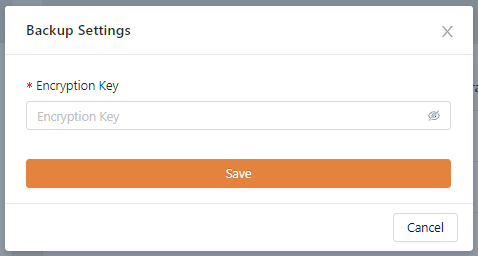
Set the encryption key. The minimum length for the encryption key is 8 characters. Click Save.
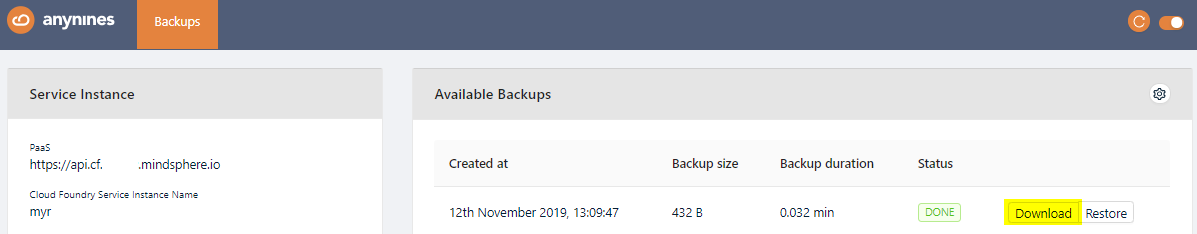
The newly created backup will now show a Download button. Click this button to download a backup.
Note
If you change your personal encryption key, you will no longer be able to download the performed backups encrypted with your old personal encryption key.
Decrypting Backup Files¶
With the file downloaded, you can decrypt it with the following command:
cat <encrypted-backup-file> | openssl enc -md md5 -aes256 -d -pass 'pass:<encryption-key>' > <decrypted-backup-file>.gz
The file will still be compressed, so it is required to decompress it:
cat <decrypted-backup-file>.gz | gunzip -c > <backup-file-name>
Every service creates the backup according to its architecture (single vs cluster) and backup type (logical, continuous archiving etc).
Each service provides tools that handle the data by itself. For this reason, the output of this command can be a still zipped file, POSIX tar archive, a binary file, or a plain text file.
You can also check the header of the file to decide how to decompress it.
file <backup-file-name>
| Output | Archive-Type | How to extract |
|---|---|---|
POSIX tar archive (GNU) | tar-archive | tar -xvf <backup-file-name> |
gzip compressed data | gzip-file | gunzip <backup-file-name> |
data | - | It's ready to use as plain text data or as binary. |
The output of this command can be multiple files.
At this point, it is required to local backup ready to be manually restored in another place.
Except where otherwise noted, content on this site is licensed under the Development License Agreement.